The U.S. Department of Defence tightens the screws on cybersecurity which has notified that it’s working on and will soon update and review compliance with contractors. In addition, IT will consider the actions taken to meet cybersecurity standards. With so many breaches last year, the concerned bodies and DOD are quite serious about the new regulation. So, have a look at how the U.S. Department of Defence tightens the screws on cybersecurity compliance.
All the details About the U.S. Department of Defence Tighten the Screws on Cybersecurity Compliance.

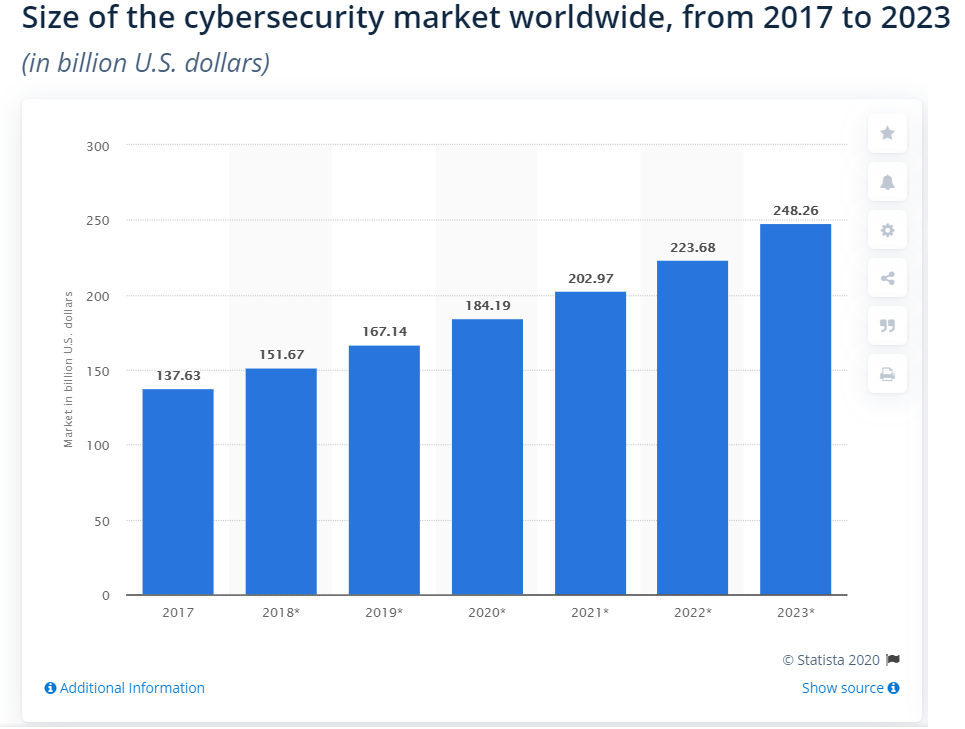
U.S. Department of Defence tightens the screws on cybersecurity compliance and the evidence is CMCC 2.0 in 2021, it’s no secret that DoD is working to keep cybersecurity very strong so there is no leak of any sensitive information that can work against the nation. With a 58.44 million dollar budget for IT and cybersecurity, the Government is taking every step to execute new actions.
So, firstly the DoD is adopting ways to ensure that contractors managing covered defense information (CDI) have proper regulations to match with cybersecurity standards found in Special Publication (SP) 800-171 of the National Institute of Standards and Technology (NIST).
In addition, to meet this guideline, the DoD announced a new mandate in November 2021. It required contractors to fill a score into the Vendor Performance Risk System (SPRS) that would inform them about their current compliance with controls 110 of the NIST SP 800-171. This is incorporated in parts 252.204-7019 and 252.204-7020 of the Federal Defence Procurement Regulation Supplement (DFARS).
Earlier, CMMC and SPRS, the DoD issued DFARS 252.204-7012, which asked contractors to sign with security controls s 110 of NIST SP 800-171. But, DoD is not sure if this requirement is met or not. As a result, the new memorandum is the DoD’s endeavor to bridge the void until all contractors have to document SPRS scores and receive CMMC certification.
Highlights of the Notice
The memorandum is entitled “Contractual resources to ensure compliance of the contractor with supplementary clause 252.204-7012 of the federal defense procurement regulation, for contracts and orders not subject to clause 252.204-7020; and additional considerations on publication special from the National Institute of Standards and Technology 800-17171 Department of Defence Evaluations.”
“The DoD reiterates the responsibility of contractors to comply with NIST SP 800-171 (in case they have information systems containing CDI) and the resources that the Government has if a contractor does not comply with NIST SP 800-171. Instead, the DoD refers to the breach as a “material breach.” This is necessary because the “material breach” is a requirement for claims under the False Claims Act. The memorandum for the U.S. Department of Defence tightens the screws on cybersecurity compliance and sets out potential resources that include:
- withholding of progress payments
- prior contractual options
- the complete or partial ending of the contract
Wrapping Up
The importance of cyber security in business is immense, and now DoD, with other bodies, is making sure that all the contractors accept the rules. It will include bringing new tech and capable employees and abiding by all the rules to avoid any breach. So, keep reading to learn all the updated news about the U.S. Department of Defence tightening the screws on cybersecurity compliance and future regulations so that you comply with them at the earliest.



